Embedded System Security
November 17, 2022
Embedded system security is a tactical method of defending software operating on embedded systems against assault. An embedded system is hardware that can be programmed and has a simple operating system and software.
Security for embedded systems offers safeguards to protect a system from all forms of hostile activity. Learn about software and physical security, embedded systems security, associated security terminologies, and four security-related characteristics of embedded systems in this section.
Embedded systems are designed to carry out a particular purpose or set of functions. Embedded systems are exceptionally dependable since they are used in consumer electronics, process control systems, aviation, in-car systems, and many more applications. However, their compact size and constrained computational power might provide security difficulties for designers and developers.
Historically, embedded systems were often designed to have a life cycle of at least 15 years since the firmware in such systems might be difficult (or impossible) to upgrade. However, the nature of embedded systems is evolving due to the internet of things (IoT), and there are an exponentially increasing number of potential attack vectors. Today, everything from smart thermostats to industrial control systems may be taken over by hacking an embedded system in an intelligent device.
Similar to security in most IT disciplines, embedded system security demands a top-to-bottom strategy that considers security concerns even at the design stage. The cost of an attack on an embedded system, the cost of an attack, and the number of potential attack channels should all be considered while thinking about security.
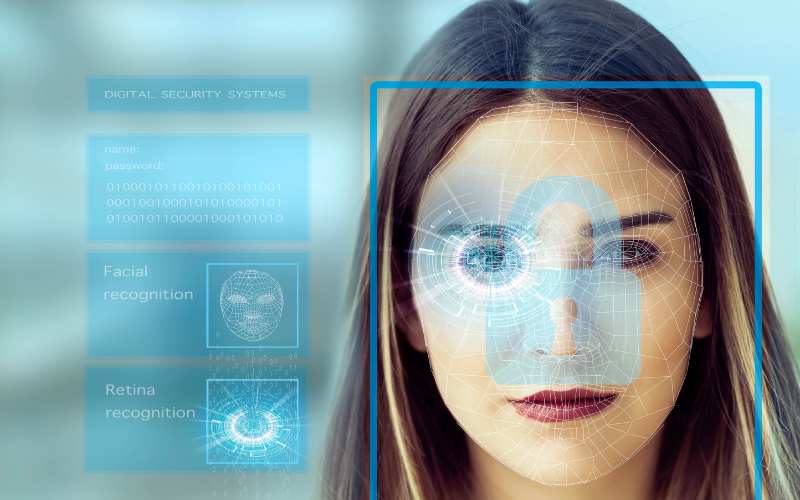
Physical security and software security are the two forms of security that apply to embedded systems.
Physical security
It keeps an unauthorized individual on-site from accessing an embedded device, physically harming it, or stealing it. Examples include closed doors and security cameras. Access to essential locations and equipment is restricted by physical security. Physical security may also refer to features of a particular device, such as tamper-resistant memory, protected key stores, immutable memory technologies, security enclaves to guard essential data and code, and refusal to hold safe bootloader keys.
Software security
Software security controls and reacts to harmful activity that occurs in the system at both the startup and runtimes. Authenticating a device to a network, filtering network traffic, and rigorously hardening system software are only a few examples of software security features.
Many embedded systems carry out safety- or mission-critical tasks that are essential to the environment and the system’s intended use. Every industry, including aerospace, military, and home appliances, may benefit from embedded systems security. The Internet of Things (IoT) is beginning to link contemporary embedded technologies, opening up new attack vectors.
The most secure embedded system is one that is entirely isolated, followed by a system that is off. Security of embedded software was less relevant when embedded systems were isolated technological nodes with little information. Nowadays, embedded systems are often linked to a communications network, increasing the system’s vulnerability to threat actors.
Intrusion detection and intrusion prevention systems (IDPS) intercept communications defensively after the device is in the field to recognize or prevent assaults and data exfiltration. Threat hunting and security monitoring of embedded systems and IoT devices are proactive security measures used by specific systems security services.
Self-tests are another tool used to evaluate an embedded system’s security posture. Monitoring events, logging crashes and abnormalities, and sending this data to the cloud are all self-testing analytics and diagnostics software functions. The data may then be analyzed by a cloud-based system, which can subsequently take action to reduce security and safety threats.
Study Cyber Security at Cybercert. For cybersecurity courses, please visit our website, www.cybercert.ca, or call (416) 471-4545.

Lead Instructor qualified in CISSP, CCIE, and MCT with 25 years of training experience in Toronto.
Recent Posts

April 27, 2023
How to Prepare for the CISSP Exam: Tips and Resources
The Certified Information Systems Security Professional (CISSP) certification is a highly sought-after credential in the field of information security. It is a vendor-neutral certification that is recognized globally and indicates a high level of proficiency in the field of cybersecurity. Passing the CISSP exam requires a lot of dedication, hard work, and preparation. In this […]
Read More
April 25, 2023
The Best Practices and Standards for CISSP Professionals
CISSP (Certified Information Systems Security Professional) is a globally recognized certification for information security professionals. CISSP professionals are expected to possess a broad range of knowledge and skills in various security domains, such as access control, cryptography, security operations, and software development security. However, possessing knowledge and skills alone is not enough to excel as […]
Read More
April 23, 2023
How to Optimize Your Cloud Costs and Performance
In today’s world, businesses rely heavily on cloud computing to store and process their data. The cloud has become an essential part of modern computing infrastructure, providing businesses with cost savings, scalability, and flexibility. However, the benefits of cloud computing have some challenges. One of the most significant challenges businesses face is how to optimize […]
Read More